What Boards Should Evaluate When Hiring Modern CISOs
Table of Content
- Why CISO Hiring Strategy Needs to Look Beyond Technical Expertise
- Where Traditional CISO Hiring Criteria Fall Short
- How the CISO Mandate Is Expanding Around Identity, Governance, and Resilience
- Cybersecurity Leadership Assessment: How to Test Judgment, Influence, and Clarity
- Common CISO Hiring Mistakes Boards Should Avoid
- Building a More Adaptive CISO Hiring Strategy
- FAQs
Four Key Takeaways
- Technical expertise is the baseline for any CISO appointment, not the differentiator. Boards must also evaluate business-risk judgment, identity and access governance, cross-functional leadership, and board-level communication.
- Traditional hiring filters such as certifications, sector familiarity, and breach exposure are useful but incomplete. The gap between security experience and enterprise risk leadership is where most CISO hiring decisions fall short.
- Strong CISO evaluation uses scenario-based assessment to test how a candidate decides, influences, and communicates under real conditions. What they did during an incident, how they governed access environments, and how they spoke to a board will reveal far more than a credentials review.
- Before the search begins, boards must define what risks the CISO will own, which decisions they can influence, and what success looks like in the first 12 to 18 months. A brief built around the organization’s actual risk environment will consistently deliver a stronger hire.
Why CISO Hiring Strategy Needs to Look Beyond Technical Expertise
The CISO role has always demanded technical depth. That has not changed. What has changed is the weight boards and executive search committees now place on everything that sits around that technical core.
A CISO is still expected to understand security architecture, control frameworks, incident response, and threat detection. These are baseline qualifications, not differentiators. The sharper question today is whether a candidate can connect security risk to business continuity, regulatory exposure, and executive decision-making in a way that actually moves the organization forward.
KPMG’s On the 2026 Board Agenda highlights that boards are expected to assess cybersecurity governance frameworks, monitor AI strategy, consider data governance adequacy, and track technology-related talent needs, all as board-level responsibilities. This signals a clear shift: cybersecurity is no longer a function that operates separately from governance and strategy. It sits at the center of both.
A sound CISO hiring strategy, therefore, cannot stop at evaluating tools experience or breach history. It must assess the candidate’s ability to operate across the full scope of what boards now expect from cybersecurity and information security leadership.
Where Traditional CISO Hiring Criteria Fall Short
Most CISO searches begin with the same checklist: technical depth, certifications such as CISSP or CISM, experience with specific tools or frameworks, familiarity with the sector, and exposure to security incidents. These are reasonable starting points, and no credible CISO hiring criteria should discard them entirely.
The problem is not what these filters capture. It is what they miss.
A candidate who scores well on technical qualifications may still struggle to explain a regulatory exposure to the CFO, influence a CIO’s procurement decision, or earn the confidence of a board that needs to understand risk in business terms. Technical experience tells you what a candidate knows. It does not tell you how they lead, communicate, or make decisions when there is no clean answer.
A University of Kansas and IBM Center for Business in Government study found that none of the top 10 skills required for senior security leaders are purely technical. Communication, collaboration, policy development, and strategic management consistently rank as critical. Yet many executive searches continue to prioritize tool experience and sector familiarity over these qualities.
The gap between security experience and enterprise risk leadership is real. Boards that treat the two as equivalent tend to hire strong security operators who are underprepared for the full scope of the role.
How the CISO Mandate Is Expanding Around Identity, Governance, and Resilience
The CISO role has not changed overnight. The expansion has been gradual, and it is now visible across three distinct layers.
Identity and Access are Becoming More Complex
NIST SP 800-207 on Zero Trust Architecture describes resource and data security as extending across both person and non-person identities, covering credentials, access management, operations, endpoints, and hosting environments. This framing matters for CISO hiring. As organizations increasingly depend on automated workflows, AI agents, vendor integrations, and machine-to-machine interactions, the number of non-person identities in any environment has grown significantly.
Identity and access governance leadership is no longer a sub-function within IT. It is a core operating responsibility of the CISO. Candidates who have only managed human-user access programs will find the scope of modern identity environments considerably broader than their experience reflects.
Governance Now Extends Beyond Security Controls
KPMG’s On the 2026 Board Agenda notes that boards should assess whether cybersecurity governance frameworks are keeping pace and should also monitor AI strategy, data governance, and technology-related workforce needs. This positions governance not as an audit exercise but as an ongoing board-level priority that the CISO must feed with structured, evidence-based reporting.
The CISO who can connect security practices to data governance, regulatory posture, and workforce decisions will carry considerably more influence in the boardroom than one focused solely on security controls.
Resilience Expectations are Becoming Broader
The World Economic Forum’s Global Cybersecurity Outlook 2026 identifies accelerating AI adoption, geopolitical fragmentation, and widening cyber inequity as forces reshaping the global cyber-risk environment. For CISO hiring purposes, this means cyber resilience leadership must be assessed as a strategic capability, not just an incident-response skill.
Microsoft’s research reinforces this: organizations that separate security from business strategy are treating resilience as a reactive state rather than a built-in operating capability.
Boards should look for CISOs who treat resilience as something designed into the organization, not bolted on after an incident.
1. Business-risk Translation
Can the candidate explain cyber exposure in financial, operational, reputational, or regulatory terms? KPMG’s Cybersecurity Considerations 2025 positions cybersecurity not as a technical afterthought but as a foundational principle of sustainable value creation, noting that organizations neglecting integrated security governance face measurable financial and reputational consequences.
A candidate who can only describe risk in technical language will struggle to influence decisions where priorities are set in business terms. Boards should ask candidates to walk through a specific instance where reframing a security risk changed an executive or board-level decision.
2. Identity and Access Governance Maturity
The identity environment a modern CISO must govern now spans vendors, privileged accounts, system identities, and automated workflows, well beyond traditional user provisioning.
Boards should assess whether candidates have actually operated across this breadth, including non-person entities and machine-to-machine access, not just managed standard employee access within a single environment.
3. Cross-functional Operating Ability
KPMG’s On the 2026 Board Agenda identifies AI strategy, data governance, cybersecurity, and technology-related workforce needs as interconnected board-level priorities. A CISO who cannot work across the CIO, CTO, legal, compliance, finance, and HR functions will consistently create gaps in exactly these areas.
The strongest candidates will have clear evidence of influencing decisions outside their own function, not just enforcing policies within it.
4. Incident Judgment
Breach experience is frequently listed as a hiring signal. It should not be taken at face value. The relevant question is not whether the candidate was present during an incident, but what decisions they made, what trade-offs they navigated, and how they communicated with stakeholders under pressure.
A candidate who oversaw a process without real decision authority is not equivalent to one who led the business response, managed board-level communication, and drove recovery priorities. Boards should probe this distinction directly.
5. Governance Discipline
KPMG’s Cybersecurity Considerations 2025 report calls for formal governance processes that clearly define accountability and decision-making authority for CISOs, particularly given the growing regulatory scrutiny across industries. A CISO who treats governance as an administrative task rather than a strategic responsibility will create the visibility gaps boards can least afford.
The right candidate connects security practices to policy, compliance reporting, board updates, and clearly defined risk ownership across the organization.
Build a stronger CISO search with Vantedge Search.
Cybersecurity Leadership Assessment: How to Test Judgment, Influence, and Clarity
Knowing what to look for is only half the task. The harder part is designing an evaluation process that surfaces genuine capability rather than polished presentation. Titles, logos, and rehearsed answers can mask the absence of real judgment, and the cost of that error at the CISO level is significant.
The WEF’s Global Cybersecurity Outlook 2026 found that cybersecurity priorities diverge sharply between the boardroom and the front line, with CEOs focused on cyber-enabled fraud and reputational exposure while CISOs remain anchored to ransomware and supply chain resilience. This gap is not just a communication problem. It signals that many CISOs have not yet developed the habit of translating their concerns into the language their boards actually use.
A structured cybersecurity leadership assessment should move beyond credentials and use scenario-based discussion to test how a candidate thinks and decides under real conditions. The following prompts are practical starting points:
- On business trade-offs: “Describe a cyber-risk decision where the technically safest option was not the most practical business option. How did you handle the trade-off?” This reveals whether the candidate can hold both security and business priorities simultaneously, without defaulting to one at the expense of the other.
- On board communication: “How have you explained cyber exposure to a CEO or board without relying on technical language?” Strong candidates will give a specific example with a specific audience and a specific outcome. Vague answers signal a gap.
- On identity and access governance leadership: “How have you governed access across employees, vendors, systems, or automated workflows?” This tests whether the candidate has genuinely operated in complex, multi-entity access environments.
- On resilience: “What evidence would show that a security program improved resilience, not just compliance?” This distinguishes candidates who build genuine organizational capability from those who fulfil reporting requirements.
WEF’s Elevating Cybersecurity 2025 report reinforces that boards must create direct lines of communication that elevate cybersecurity to a strategic concern, and that the CISO’s mandate is to provide a genuine view of the organization’s cyber-risk posture.
An assessment process that tests for this ability, rather than assuming it based on seniority, is what separates a sound CISO search from a costly one.
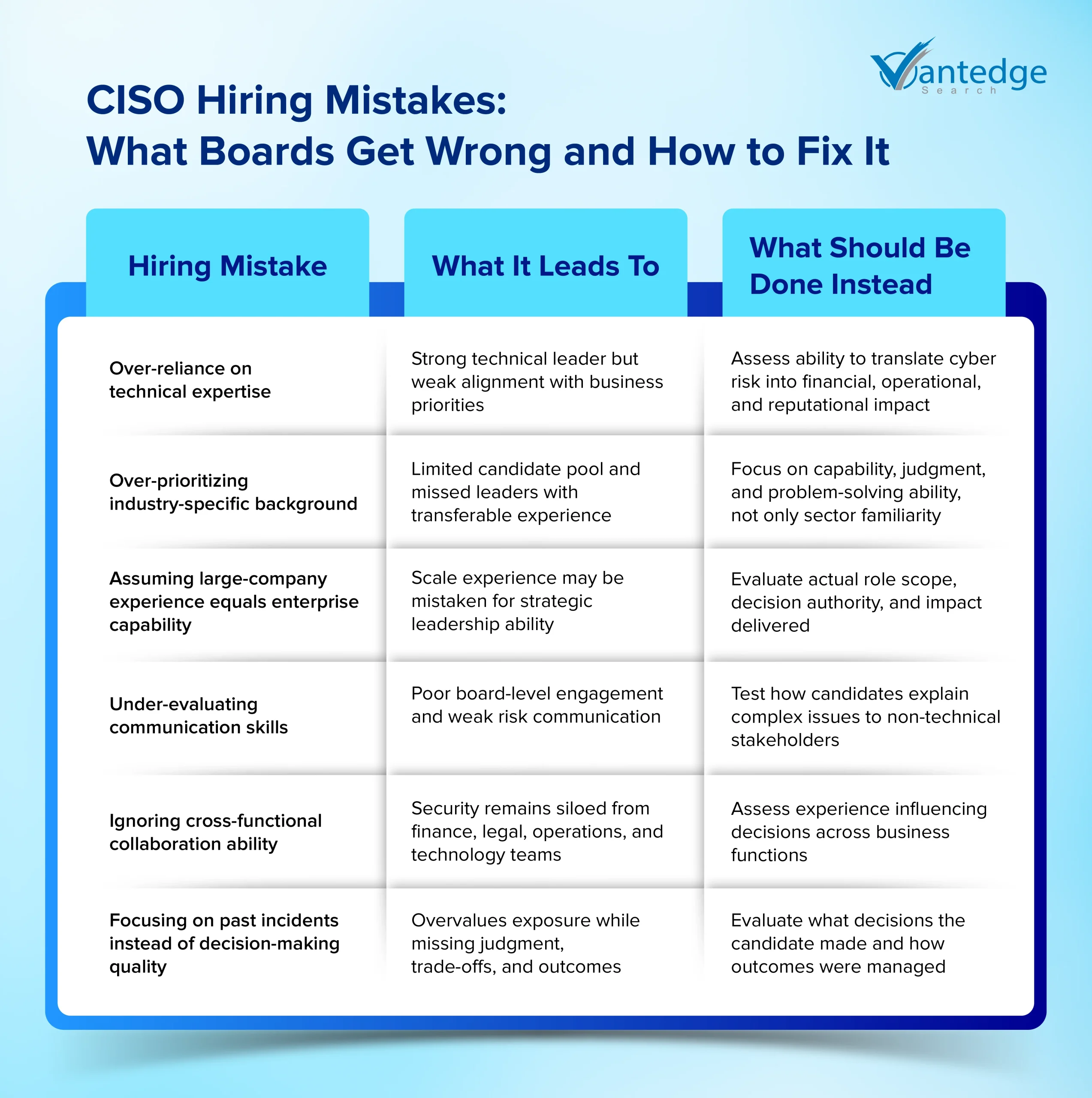
Common CISO Hiring Mistakes Boards Should Avoid
Common CISO hiring mistakes rarely look like errors in the moment. They look like reasonable decisions made with incomplete criteria. The following patterns appear consistently in CISO searches and carry measurable risk for the organization.
- Overvaluing technical depth while under-testing business communication. A candidate who can architect a zero-trust environment but cannot present a credible risk position to the board will struggle to hold influence where it matters most. Technical strength is necessary; it is not sufficient.
- Treating industry familiarity as a substitute for leadership capability. Sector experience can accelerate onboarding, but it does not guarantee strategic judgment. Boards that limit their candidate pool to a single industry often pass over stronger leaders with directly transferable capability.
- Assuming large-company experience equals strong operating judgment. Scale of environment and quality of decision-making authority are not the same thing. A candidate from a large organization may have operated within a narrow remit. Boards should assess actual scope, not just the size of the employer.
- Valuing breach exposure without examining the candidate’s decision role. Being present during a major incident is not the same as leading the response. The relevant evidence is what decisions the candidate owned, not which incidents appeared on their watch.
- Failing to test cross-functional influence. A CISO who has not built working relationships across legal, finance, operations, and technology will create a security function that remains siloed from the decisions that shape enterprise risk.
- Using vague “strategic CISO” language without defining the organization’s actual needs. Before a search begins, boards should be clear on what risks the CISO will own, which decisions they can influence, and what success looks like in the first 12 to 18 months.
The hiring mistakes outlined above often stem from an incomplete picture of what the CISO role looks like today. The role has shifted significantly, and the expectations boards now bring to a CISO search reflect that. (For a detailed look at how cybersecurity leadership is moving to the center of board strategy, read our blog: CISO Role in 2026: Why Cybersecurity Is Moving to the Boardroom.)
Building a More Adaptive CISO Hiring Strategy
The CISO role is not moving away from cybersecurity and information security expertise. It is expanding around it. Identity governance, regulatory accountability, board-level communication, cross-functional influence, and resilience planning are not additions to the role; they are now central to it.
As AI adoption, automation, and regulatory pressure continue to develop across industries, the demands placed on cybersecurity leadership will follow. Boards that rely on static hiring criteria will find themselves appointing candidates who are well-qualified for a version of the role that no longer reflects the full scope of what is required.
The strongest CISO hiring strategy is one that remains adaptive, asking not only who has the right technical background, but who can translate security into decisions, governance, resilience, and enterprise trust. That question, asked rigorously and assessed with clear evidence, is what defines a search that delivers lasting value.
If your organization is preparing for a CISO search, partner with Vantedge Search today. We help boards and leadership teams define the right brief, evaluate the right candidates, and make hiring decisions with greater clarity and confidence
FAQs
A CISO hiring strategy is the structured process through which boards and search committees define the candidate profile, set evaluation criteria, and assess fit for the role. It should be built around the organization’s actual risk environment, testing not just technical qualifications but business-risk judgment, governance discipline, and cross-functional influence.
Effective evaluation moves beyond certifications and breach history to assess how a candidate thinks, decides, and communicates under real conditions. Scenario-based prompts, such as asking how they explained cyber exposure to a board or managed a trade-off between security and business priorities, reveal judgment more reliably than credentials alone.
The most common CISO hiring mistakes include overvaluing technical depth while under-testing communication, treating sector familiarity as a substitute for leadership capability, and assuming large-company experience reflects strong operating judgment. Boards that fail to define the organization’s specific risk environment and success criteria before the search begins tend to compound all of these errors.
A modern CISO needs technical security expertise as a foundation, alongside the ability to translate cyber risk into business terms, govern complex identity and access environments, and communicate credibly at board level. As regulatory expectations and AI-driven complexity grow, resilience-oriented thinking and cross-functional influence are equally critical.
Most CISO hiring decisions fail when searches prioritize technical depth or sector familiarity over leadership capability and business alignment. Without scenario-based assessment and a clearly defined brief covering risk ownership, stakeholder scope, and success criteria, gaps in judgment and communication only become visible after the appointment.


Leave a Reply